IT Consulting
We connect your IT systems, processes and people
Our consultants support companies from all industries on their digital journey by providing comprehensive advice in the areas of strategy and design, architecture, implementation, infrastructure, and security.
From developing and implementing IoT and cloud strategies to creating and executing technical security concepts, audius consultants are the ideal partner for any project.


+49 (7151) 369 00 - 316
Biographie
Michael Mederer ist seit mehr als 20 Jahren in unterschiedlichen Funktionen bei audius tätig. Heute berät er Kunden aus unterschiedlichen Branchen als Senior IT-Consultant u.a. in den Bereichen IT-Infrastruktur, IoT & Cloud Strategien, Security Konzepte.
Benefits
benefits
Normaler Abstand nach oben
Normaler Abstand nach unten
Product information
product-information
Network
- WAN/Internet access, connections and concepts
- Network and WLAN architecture and implementation
- Firewall and network security (segmentation, VLANs, DMZ, load balancing, WAF, encryption)
IoT and cloud strategies
- Technology consulting (private cloud, public cloud, hybrid cloud)
- Cloud model consulting (IaaS, PaaS, SaaS)
- Product and license consulting
- Access, training, and implementation
- Cloud strategy development, architecture, and implementation
Basic infrastructure
- Server and storage architecture, consulting and implementation
- Platform and virtualization solutions
- Windows and Linux installations / setup and application design
- High availability solutions
Security concepts, solutions and implementations
Segmentation, endpoint security, vulnerability analysis, AD security, authentication/multi-factor authentication (MFA), e-mail security, e-mail encryption, data center security, VPN, SASE solutions, and much more
Basic services and technologies
Active Directory, GPO, DNS, DHCP, NTP, mail, file services, authentication, web services, backup, certificates, PKI, logging, monitoring, asset and patch management, MDM, and much more
Our programs
programs

To help you reach your goal as quickly as possible, we have developed the following consulting programs based on best practices. Because every company has its own IT structures and guidelines, our assessments and audits focus on developing an operational concept that is specifically designed for your company and its needs.
More and more companies are moving to the cloud. To make the transition as smooth as possible, there are some issues you need to keep in mind. Our consultants can help you with the ACRC, which analyzes your existing infrastructure, processes, and security measures to generate an assessment of your “cloud maturity.”
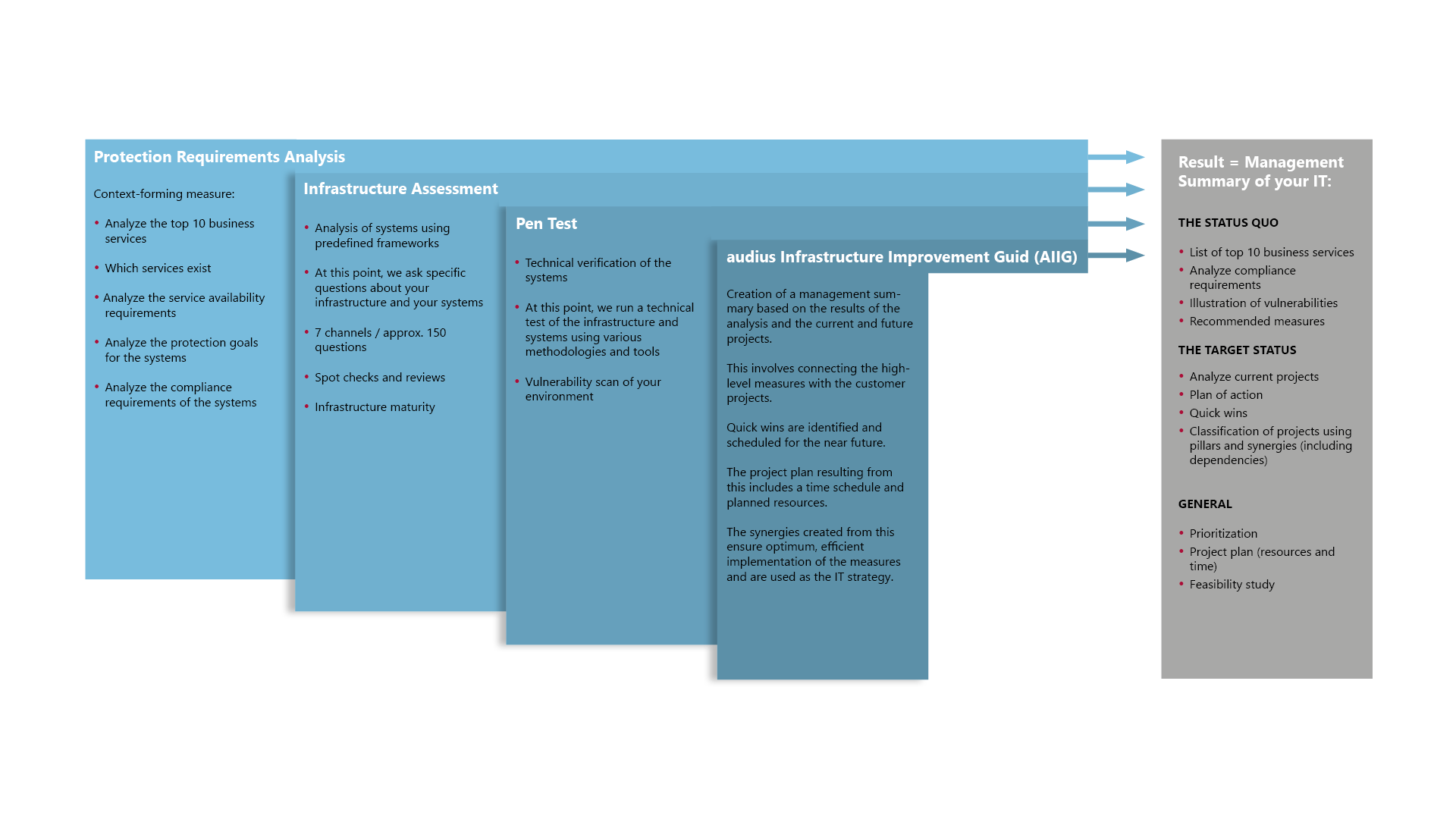
The AIIG includes a step-by-step plan, which consists of the results of the assessments (AISA) as well as current and future IT projects. Our consultants place the high-level measures in the context of the customer’s projects. They identify quick wins, schedule them in a timely manner, and classify and prioritize projects. The resulting project plan includes detailed time and resource planning.
The synergies achieved in this way ensure that your measures and strategies are implemented optimally and efficiently.
Together, we conduct an audit that includes a protection requirements analysis, an infrastructure assessment, and a penetration test. We evaluate the results and point out any vulnerabilities or “findings.” We then compile the resulting measures into a report, on the basis of which we provide you with an advanced IT strategy recommendation.
Trends und Insights
Normaler Abstand nach oben
Normaler Abstand nach unten
Partnerships / Memberships
partner
Normaler Abstand nach oben
Normaler Abstand nach unten
















Downloads
downloads
Normaler Abstand nach oben
Normaler Abstand nach unten
How can I help you?
kontakt
Normaler Abstand nach oben
Normaler Abstand nach unten
+49 (7151) 369 00 - 316
Biographie
Michael Mederer ist seit mehr als 20 Jahren in unterschiedlichen Funktionen bei audius tätig. Heute berät er Kunden aus unterschiedlichen Branchen als Senior IT-Consultant u.a. in den Bereichen IT-Infrastruktur, IoT & Cloud Strategien, Security Konzepte.